The trouble with Ostarine: Jimmy Wallhead’s
16th March 2018
Features

Investigators in the United Kingdom and the United States have found that computer hackers working for the main intelligence directorate of the Russian military (GRU) instigated sophisticated campaigns designed to disrupt the PyeongChang 2018 and Tokyo 2020 Olympics. The US Department of Justice (DoJ) indicted six GRU operatives for using a number of techniques to deploy malware – nicknamed ‘Olympic Destroyer’ by researchers – that disabled thousands of computers used in the organisation of the PyeongChang 2018 Winter Olympics.

GRU agents allegedly planned a similar performance at the Tokyo 2020 Olympics, before they were postponed. The GRU conducted ‘cyber reconnaissance’ against Tokyo 2020 officials and organisations; logistics services; and sponsors, the UK’s Foreign Office announced. The UK’s National Cyber Security Centre (NCSC) said its assessment revealed ‘high confidence’ that both attacks were carried out by the GRU’s Main Centre for Specialist Technologies (GTsST), also known as Sandworm and VoodooBear.
This is not the first time that the DoJ has indicted GRU agents in connection to attacks on the integrity of sport. In 2018, it named seven GRU agents as being responsible for the ‘Fancy Bears’ hacks into anti-doping systems.

Although none of the GRU agents are the same, both DoJ indictments involve operatives working for GRU Unit 74455, located at 22 Kirova (Кирова) Street in the Moscow suburb of Khimki (Химки). This is understood to contain the headquarters of the GTsST, the same GRU Unit and same tower block that the DoJ alleges to be the headquarters of Russian attempts to manipulate the 2016 US Presidential election.
Both DoJ indictments also involve attempts to disrupt Organisation for the Prohibition of Chemical Weapons (OPCW) investigations into the poisoning of Sergei Skripal and others in the UK. Yesterday’s indictment (PDF below) also reveals that GRU operatives attempted to hack into the UK’s Defence Science and Technology Laboratory (DTSL) in Porton Down in order to disrupt its investigations into the Skripal poisonings.
Three of the six indicted GRU hackers registered cars at 22 Kirova Street discovered Aric Toler, a journalist with Bellingcat. A subsequent search found 47 people had registered cars at the same address. A similar operation performed by Bellingcat in 2018 found 305 people had registered their cars at another GRU address, including Aleksei Morenets (Алексей Моренец). He was one of seven GRU operatives named in the 2018 indictment as being behind Fancy Bears and its attempts to dupe people into believing that doping in sport is widespread in ‘western’ countries (click here for analysis).
An example of how bumbling the Russian state is: of the six indicted hackers, three registered their cars to their military unit's address in Moscow. If you search for all of the people registering their cars to this address, you get 47 results – all probably GRU hackers. pic.twitter.com/G8SKJQ2WFT
— Aric Toler (@AricToler) October 19, 2020
Russia has denied being behind the cyberattacks. ‘Quite obviously, the task that London is setting itself is not to get to the bottom of the alleged cyber incidents, but to use this issue as part of a deliberate disinformation campaign aimed at discrediting Russia’, read a statement from Russia’s UK Embassy. ‘The current cycle of this campaign coincides with the US Presidential election. The purpose is clear: to create extra grounds for accusing Russia of “meddling in the election” […] At the same time, references to the Olympic Games in South Korea and Japan seek to spoil Russia’s constructive relations with these two countries.’
Russia’s US Embassy posted a similar statement on Twitter. ‘It is absolutely obvious that such news breaks have no bearing on reality and are aimed at whipping up Russophobic sentiments in American society, at launching a “witch hunt” & spy mania, which have been a distinctive feature of the political life in Washington for several years’, it read. ‘Russia does not and did not have intentions to engage in any kind of destabilising operations around the world. This does not correspond to our foreign policy, national interests, or our understanding of how relations between States are built. Russia respects the sovereignty of other countries and does not interfere in their affairs.’
It is absolutely obvious that such news breaks have no bearing on reality and are aimed at whipping up Russophobic sentiments in American society, at launching a ‘witch hunt’ & spy mania, which have been a distinctive feature of the political life in Washington for several years. pic.twitter.com/kzQOC7RZQp
— Russian Embassy in USA ?? (@RusEmbUSA) October 20, 2020

The six defendants began spearfishing in November 2017 both by creating emails and by mimicking International Olympic Committee (IOC) and PyeongChang 2018 email addresses in order to distribute malware to the computers of IOC, PyeongChang 2018 officials and their commercial partners, the DOJ alleges. Domains similar to official bodies were registered in order to make emails appear official. This included an email purporting to be a warning about an earthquake that installed malware on the opener’s computer.
Spearfishing attacks directed at Omega, the timekeeping partner for PyeongChang 2018, enabled the GRU to install malware that allowed it to create email accounts, alleges the DoJ. It then used this ability to send further spearfishing emails purporting to be from the CEO of Omega. Three mobile applications mimicked the names of legitimate Korean services, the DoJ alleges.
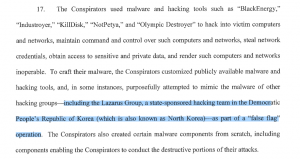
The DoJ alleges that the purpose of this was to install malware on the devices of organisers of the PyeongChang 2018 Winter Olympics. As the Opening Ceremony to the Games begun, it is alleged that the GRU activated its malware, rendering computer systems inoperable. How this was accomplished is complicated, but is detailed in full in the DoJ indictment (p.59-63). The GRU then attempted to obfuscate the source of the malware, attempting to emulate malware used by North Korea’s Lazarus Group, the DoJ alleges.
If investigations are accurate it would appear that once again, Russia’s strategy for dealing with sporting sanctions is to attack the sporting community. When sanctioned by the World Anti-Doping Agency (WADA) for State doping, it deployed a hacking team (Fancy Bears) in an attempt to convince the world that other countries were abusing the therapeutic use exemption (TUE) system. The reputations of many athletes, who had legitimate reasons for a TUE, were compromised.
When sanctioned by the IOC for State doping, Russia sent GRU operatives to the Rio 2016 Olympics and to WADA conferences to conduct ‘on-site’ hacking operations. When such sanctions were not lifted for PyeongChang 2018 and Tokyo 2020, it appears that its strategy was again to deploy GRU agents to attack those specific events.
Once again, sport will be rightly shocked by Russia’s duplicity, which has also involved:
• Adjustments to the Moscow Laboratory Information Management System (LIMS) in an attempt to hide State doping;
• Allegations that athlete appeals against doping sanctions are financed via the Russian State;
It appears that at least 13 GRU operatives were employed by the Russian State to conduct such operations, over a number of years. This costs money. Fancy Bears also cost money. So did manipulations to the Moscow LIMS. So does any financing of athlete appeals against doping sanctions via the Russian State. So does the Russian Anti-Doping Agency’s (RUSADA) appeal against WADA’s decision to declare it non-compliant with the World Anti-Doping Code for a four year period.
This apparent strategy of attacking those sanctioning Russian sport must have cost Russia millions. It would appear it has got Russia nowhere. If anything, sanctions have been lengthened and world sport is now more suspicious of Russia. The onset of Covid-19 means that recession is perhaps imminent – particularly in sport. Will the Russian State continue to finance such an apparently pointless campaign? Will Russia’s people continue to let it?
Athletes have been medically harmed due to sport’s limits on testosterone in its female category,...
• Twenty three athletes from 14 countries, competing in 11 sports, were involved in anti-doping...
• Twelve athletes from nine countries, competing in seven sports, were involved in anti-doping proceedings...